How to Use a Firewall for Network Traffic Analysis and Behavioral Detection
This post is also available in: 日本語 (Japanese)
On March 17, we hosted a webinar called “Leverage Your Firewall to Expose Attackers Hiding in Your Network” to share tips on how you can use your firewall for network traffic analysis. We’ll go into lots of detail on scenarios like the ones described below and the benefits for your organization. Register today!
 The ultimate goal of cybersecurity teams is to prevent all attacks. However, even when the best defenses are in place, adversaries can launch unlimited intrusion attempts, consequence-free, until they find a way in. Gaining visibility into attacks that have successfully penetrated your network – including understanding how attackers got there and what damage they’ve done – is a key component of overall security.
The ultimate goal of cybersecurity teams is to prevent all attacks. However, even when the best defenses are in place, adversaries can launch unlimited intrusion attempts, consequence-free, until they find a way in. Gaining visibility into attacks that have successfully penetrated your network – including understanding how attackers got there and what damage they’ve done – is a key component of overall security.
Network traffic analysis (NTA) – sometimes called network detection and response – is one such tool that provides that visibility. NTA is a category of technologies designed to provide visibility into things like traffic within the data center (east-west traffic), VPN traffic from mobile users or branch offices, and traffic from unmanaged IoT devices. NTA is also a key capability of Cortex XDR that many network teams don’t realize they have access to.
Any organization that uses Palo Alto Networks, Cisco, Check Point and/or Fortinet firewalls can send their next-generation firewall logs – including traffic logs, enhanced application logs, threat logs and URL filtering logs – to Cortex XDR. Then Cortex XDR applies behavioral analytics and machine learning to the data to detect stealthy attacks like lateral movement or exfiltration. Cortex XDR also groups related alerts into incidents to reduce the number of individual alerts that security analysts need to review.
This allows network security teams to:
- Detect and stop active attackers operating in the network.
- Improve visibility into east-west traffic.
- Protect managed and unmanaged devices, eliminating network blind spots.
- Stop malware, targeted attacks and insider abuse, with detection of all network-based tactics and techniques including command and control, lateral movement, exfiltration and malware activity.
Palo Alto Networks customers can simply add these capabilities as a subscription to their Next-Generation Firewalls without needing to deploy extra software or network appliances.
Organizations can take this to the next level by connecting their firewalls to other security sensors throughout their organization. The ability to connect network data to endpoint and cloud data is one of the core benefits of XDR. This cross-infrastructure visibility lets security analysts (and their analytics tools) quickly and confidently answer questions like, “What’s happening on an endpoint that is making a network alert fire, and is it problematic?”
These seemingly basic questions are not basic at all when you have siloed tools that each offer only partial visibility. We’ve heard from customers that prior to XDR, they’d waste hours each day manually tracking suspicious activity on an endpoint only to find out that adversaries were blocked by the firewall before they could access sensitive data.
Conversely, connecting your firewalls to Cortex XDR means that all of your artifact, user and computer data from across your infrastructure is extracted and stitched together with threat intel in a visualized chain of events. This fundamentally changes the process of investigating the root cause of suspicious network events.
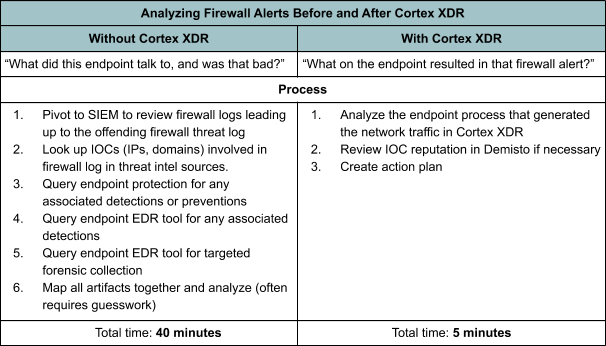
In a case study of the Palo Alto Networks Security Operations Center (SOC), SOC Manager Matt Mellen gave us a detailed rundown of what the firewall alert investigation process looked like before and after adopting XDR, and how the team was able to make that process eight times faster:
Cortex XDR gives us insight we never had before, especially around firewall-based alerts. Historically, when responding to something like a command-and-control (C2) firewall alert, it’s taken around 40 minutes to answer the question, “What did this endpoint talk to, and was that bad?” We relied on third-party threat intelligence to know if domains or hashes were bad. We would get an alert in one tool, verify traffic, turn to another tool to see if the system was online, and then to another tool to see what was causing the C2. Now, we ask, “What on the endpoint resulted in that firewall alert?” That’s a much better question – it lets us know the causality of offending firewall traffic, and we can evaluate it all in one tool within five minutes. It’s significantly more accurate and much faster to analyze compared to the former model.
As useful as it is to have this birds-eye view across your whole infrastructure, most solutions that claim to provide this level of visibility can only do so with really shallow data (e.g. SIEM), or otherwise can only see data from their own sensors (e.g. most XDR vendors). Cortex XDR is unique in its ability to extend this visibility to third-party network data with enough rich context that you can resolve the issue without having to pivot to another tool. Your security teams can connect Cisco, Check Point and Fortinet firewall data together with your Palo Alto Networks firewall, endpoint and cloud sensors to gain the benefit of Cortex XDR’s powerful machine learning, behavioral analytics and incident visualization across your entire infrastructure.
To learn more about how to use Cortex XDR to help solve your network security challenges, sign up for our March 17 webinar, “Leverage Your Firewall to Expose Attackers Hiding in Your Network.”
Related Blogs
Subscribe to the Newsletter!
By submitting this form, you agree to our Terms of Use and acknowledge our Privacy Statement. Please look for a confirmation email from us. If you don't receive it in the next 10 minutes, please check your spam folder.